VoIPmonitor released updates to both the sniffer component and the web application to address vulnerabilities that your favourite Enable Security researchers identified and reported. The sniffer component had a buffer overflow flaw that we actually abused to run arbitrary code (yes, in 2021!). The web application, on the other hand, was vulnerable to cross-site scripting introduced through SIP messages with XSS payloads - which is pretty bad.
And so, we just released three advisories to provide further details so that organisations using this software can make better informed decisions. The advisories can be found at the usual location:
- VoIPmonitor WEB GUI vulnerable to Cross-Site Scripting via SIP messages
- VoIPmonitor is vulnerable to a buffer overflow when using the live sniffer
- VoIPmonitor static builds are compiled without any standard memory corruption protection
If you’re using VoIPmonitor, our recommendations are:
- upgrade to the latest fixed versions
- build your own binaries if you want memory corruption protection
Here’s the obligatory alert popup demonstrating XSS:
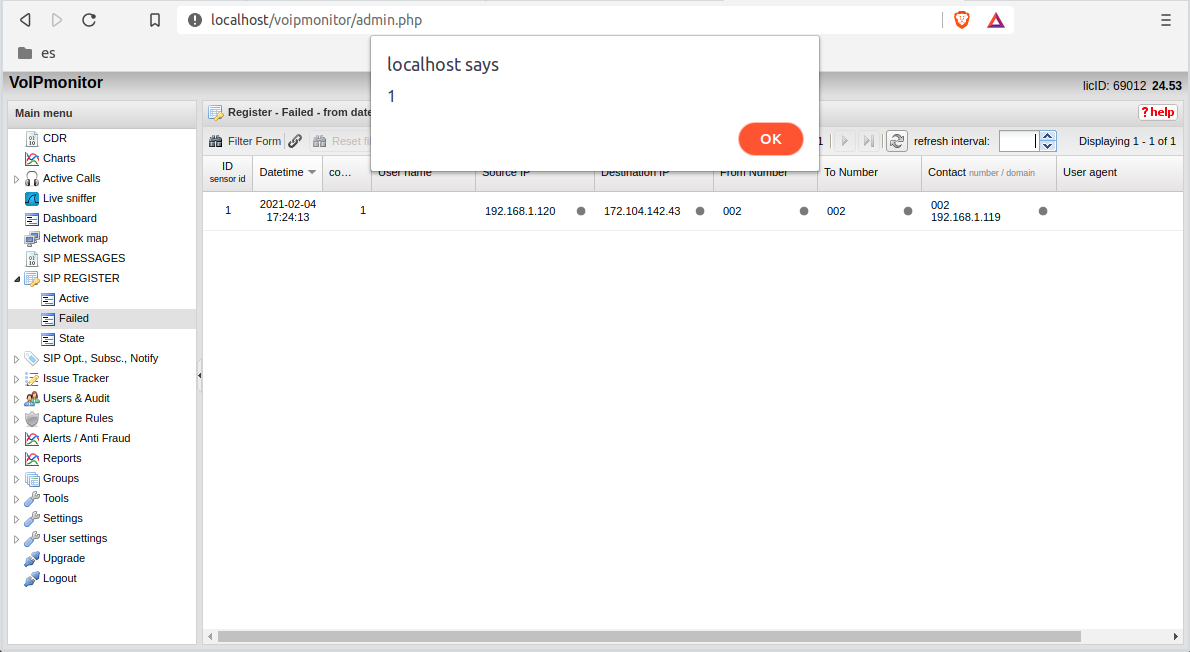
Of course, in the advisory we give an example of abusing cross-site scripting to create a backdoor administrative user too.
Full details are in the advisories but expect further details in future blog posts.