It’s the moment you’ve eagerly anticipated, that special time of the month. Yes, end of the month means salary time for many, and Halloween - but also - your favorite newsletter is out and about!
In this edition, we cover:
- A presentation by good pseudonym at DEF CON about PBX and UC hacking
- The drama that ensued with regards to FreePBX vulnerabilities
- How our customers are enjoying access to the Attack Platform
- Security fixes in WebRTC and Skype for business
- Short news including MiTM attacks on XMPP, monthly vulnerability fixes and much more!
RTCSec newsletter is a free periodic newsletter bringing you commentary and news around VoIP and WebRTC security. We cover both defensive and offensive security as they relate to Real-time Communications.
What is RTC security anyway? Real-time communications security is what determines if you can communicate in real time in a safe way - whether it be with other humans or machines.
You may sign up to receive the RTCSec newsletter here. Do:
- forward to that person who may find this newsletter particularly fruitful.
- let us know if we should include or cover any RTC security news.
To view past issues, please visit our website at https://www.rtcsec.com/newsletter.
Our news
Enable Security’s Attack Platform available to our customers
The Attack Platform allows us and our customers to run well-packaged and often custom security tests, including application-layer DDoS attacks. With the Attack Platform, this is done with the click of a button (see note below)!
We’re very excited about this as it simplifies a lot of our work and also enables our customers to run advanced security tests at their own convenience. So, we’re starting to make the Attack Platform available to our customers so that retests of vulnerabilities found during our penetration tests can be done easily and at any time.
Note: the button is not red (yet), we’re working on that ;-)
Want to know more? Reply to me directly or contact us.
What’s happening?
DEF CON 31 talk - Calling it a 0-Day - Hacking at PBX UC Systems
DEF CON 31 which happened in August this year had a great presentation titled Calling it a 0 Day - Hacking at PBX UC Systems by someone who goes by the name of Charles M. Ishihara on twitter. His presentation covered a few vulnerabilities in unified communications systems. Specifically, the presenter looked at sipXcom and FreePBX.
During his introduction to the presentation, Charles emphasized the extensive attack surface present in PBX and UC servers. For example, they might support SIP, MGCP, RTSP, have complex web management interfaces, do Fax, SMS, XMPP, proprietary protocols and so on. He finishes his introduction by highlighting that he felt he was therefore only scratching the surface. This reflects our experience when pentesting PBX systems for phone system vendors - there is always more to explore due to the large codebase, various different protocols and features - many of which have various diverse security implications.
The vulnerability in sipXcom that he disclosed is an argument injection vulnerability that’s abused through XMPP messages. In order to exploit this vulnerability, malicious actors must have the capability to send chat messages via the XMPP server containing the @call string to activate the susceptible function. This function, when triggered, uses curl in a manner that can be exploited. Such exploitation results in the execution of remote code on the server. The vulnerability is tracked as CVE-2023-25356 and we had covered it in the March edition of this newsletter.
In the case of FreePBX, since it uses ionCube to obfuscate a lot of its PHP, the presenter talks about how to deobfuscate such PHP code. He wrote a Ghidra script to deobfuscate strings in ionCube itself (not the PHP code) that otherwise make it hard to figure out how ionCube works. Once there, he could hook some strategic points and end up with de-obfuscated PHP(-ish) code that one could work with.
The security researcher analyzed the FreePBX /restapps/dphoneApi.php and although there is authentication, the username is a MAC address while the password is a hardcoded password login. To use this dphone API, you also need to make use of a user-agent header that indicates that you’re a Digium phone. Naturally, MAC addresses are not secrets and thus the presenter considers this vulnerability as an authentication bypass - which sounds just about right to us too. This authentication bypass can be chained with another vulnerability, a simple exec() remote code execution in the pbx.users.currentCalls.stopRecording method exposed by this API.
He also found other security issues in the administrative interface of FreePBX which is accessible through a low privileged user that are separate from this dphone API vulnerabilities. While the dphone API needs to be reachable to certain phones connecting to the PBX, the administrative interface is often only accessible to administrators and internal users for self-serve functionality.
Proof of concept code can be found at the presenters Github repository.
Sangoma’s responses to his security reports and queries were very limited and frustrating for the researcher. Even if they had a bug bounty page indicating that they have processes in place for receiving security reports - they actually provided no proper response, no CVEs were issued by the time of the presentation and generally, it was very discouraging. They did issue a public patch that the researcher found to be ineffective (i.e. it could be bypassed). Thus there were no proper fixes at the time of the presentation.
The presenter parted by highlighting how PBX systems have complicated user authentication models in combination with a lot of functionality that can introduce security vulnerabilities. These systems have to be exposed because they need to be accessible to their users and are generally problematic from a security point of view. Command and argument injection bugs should not be sitting there for years only to be found in opensource PBX servers in 2023.
But wait, the story does not end here!
FreePBX servers hacked in the wild! And a podcast about it
Crosstalk Solutions, who provide hosted PBX solutions, posted a Youtube video, podcast style, where they talked about how a number of their phone systems were hacked. This all happened during mid-August and they were able to detect the compromise through the use of monitoring (they use Zabbix and Grafana). They found that the firewalls on their FreePBX systems were disabled which was suspicious. Then they found cron jobs that were installed on these PBX servers that were creating backdoors on the systems. This led to root-level persistent access for the attackers.
In their analysis, they came to the conclusion that the intrusion vector was the phone apps port on the FreePBX - that is used by the phones to access visual voicemail and other features. They worked with the good folks at Clearly IP - who originally wrote FreePBX before breaking off from Sangoma - to quickly patch the system and add some extra logging to figure out what is actually going on.
The presentation at DEF CON was referenced especially because it clears up how authentication for the phone apps port was so easily bypassed (or ineffective). The podcast also blasts Sangoma’s lack of response for these vulnerability reports. Not only did they not address the vulnerabilities in time but they also removed the bug bounty page from their Wiki entirely! It is quite clear that Sangoma are not in a position to address security vulnerabilities in the FreePBX project in a timely fashion.
Finally, the podcast covers the future of FreePBX which does not look very bright. Their contention is that the FreePBX project could thrive if entrusted to an organization or community capable of effectively advancing and sustaining its development.
Sangoma issued a blog post by Lorne Gaetz that links to two advisories and that explains what happened and that the vulnerabilities were fixed. We did not review the patches for this publication - can anyone confirm if the fixes were actually effective? We’re especially interested in the ones involving authentication for the Phone Apps, which seem like a design security vulnerability. Please get in touch if you have more information.
Timeline
- 2023-05-05 security researcher sent report to Sangoma
- 2023-05-08 first response from Sangoma
- … further follow ups and tweets that mostly had no response
- 2023-05-15 patch applied by Sangoma that was bypassed by the researcher
- 2023-08-10 initial POC code uploaded to Github by the security researcher
- 2023-08-12 presentation at DEF CON
- 2023-09-05 CVE-2023-41903 reserved by Sangoma for the Phone Apps Authentication issue
- 2023-09-15 presentation published on Youtube
- 2023-09-20 blog post issued by Sangoma about the vulnerabilities and likely removed the bug bounty page
- 2023-09-28 CVE-2023-44274 reserved for the GQL token endpoint vulnerability
- 2023-10-12 podcast by Crosstalk Solutions published
Skype for Business fixes a privilege elevation vulnerability
Microsoft fixed a vulnerability that allows attackers to cause the Skype for Business server to make an HTTP request to an arbitrary address. It sounds very much like a server-side request forgery (SSRF) to us!
In fact, one of the researchers who reported this has written an extensive blog post about it.
This vulnerability report is credited to Florian Hauser (@frycos) and an anonymous contributor.
Fixes for WebRTC’s libvpx address actively exploited vulnerability CVE-2023-5217
The video codec library libvpx had a heap overflow vulnerability. According to Maddie Stone of Google, this vulnerability is being actively exploited by one of the commercial surveillance vendors (think NSO competitors). Its abuse would lead to remote code execution so it is quite a critical vulnerability. Since WebRTC depends on libvpx for the implementation of the VP9 and VP9 video codecs, it might affect all web browsers and all browser vendors have issued fixes to address this issue. References:
- https://nvd.nist.gov/vuln/detail/CVE-2023-5217
- https://groups.google.com/g/discuss-webrtc/c/ZWZcVOAq7ws/m/sWfzjgbnAwAJ
- https://arstechnica.com/security/2023/09/new-0-day-in-chrome-and-firefox-is-likely-to-plague-other-software/
Short news and commentary
- XMPP.ru MitM interception incident on Hetzner and Linode
- The XMPP servers for
xmpp.rusuffered a major man-in-the-middle attack on connections done over port 8222. Certificate transparency logs were created for exactly this sort of thing but of course the reality is much more complex than a simple technical solution. The referenced URLs provide fascinating insight into the investigation of this incident as well as recommendations for prevention of similar situations. - https://notes.valdikss.org.ru/jabber.ru-mitm/
- https://www.devever.net/~hl/xmpp-incident
- The XMPP servers for
- OpenSIPS fixed certificate verification in client mode when using wolfSSL
- It was previously assumed in the OpenSIPS’s
tls_wolfsslmodule that there is no need to enableSSL_VERIFY_PEERbecause it is on by default for client TLS connections. It turns out that thetls_wolfsslmodule was initiatingverify_modeto zero (i.e.SSL_VERIFY_NONE) by default, thus overriding the defaults set by wolfSSL. This has been fixed through a pull request by Bence Szigeti. - https://github.com/OpenSIPS/opensips/pull/3223
- It was previously assumed in the OpenSIPS’s
- USN-6422-1: Ring vulnerabilities fixed by Ubuntu
- Ring is a secure and distributed voice, video and chat platform that depends on the pjsip library that had a number of vulnerabilities addressed in the past few years. Ubuntu has finally issued an update which addresses these vulnerabilities. Unfortunately, relying on OS package updates, especially with dependencies, seems problematic for many VoIP related projects which are often receiving updates as late as a few years.
- https://ubuntu.com/security/notices/USN-6422-1
- PJPROJECT fixes a use-after-free in SRTP media transport
- Speaking of PJSIP (see Ring), if your software project relies on it - it is time to apply the patch! Software dependencies need to be kept up to date and should trigger an update in your own software. There is no release yet for this, so the patch is the way to go. Review the advisory to see if you’re affected.
- https://github.com/pjsip/pjproject/security/advisories/GHSA-f76w-fh7c-pc66
- Juniper releases two interesting advisories related to VoIP
- NSA and CISA’s top 10 misconfigurations includes VoIP equipment
- Nothing new here but good to see some recognition into the still huge problem of default credentials in VoIP equipment.
- https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-278a
- WebRTC Live Episode 85: Implementing Gold Standard Privacy and Security for Video Applications
- The next WebRTC Live episode invites Robert Strobl of Digital Samba to talk about End-to-End Encryption (E2EE) for secure and private communication during group video calls, WebRTC security, AI and quantum cryptography of course! Streams live on November 8.
- https://webrtc.ventures/webrtc-live/
Tweet of the month
We bring back the tweet of the month .. this time the award goes to:
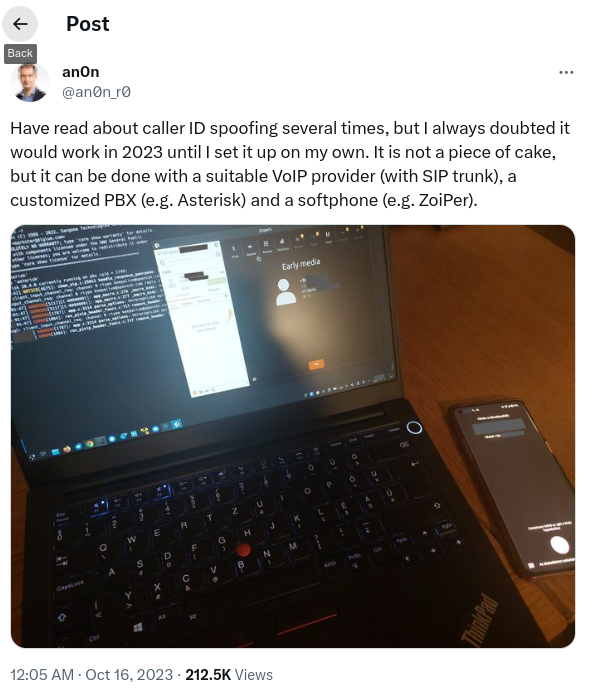
Reference: https://twitter.com/an0n_r0/status/1713677601741345117?cn=ZmxleGlibGVfcmVjcw%3D%3D
This newsletter was prepared by Sandro Gauci and the Enable Security team for the RTCSec newsletter subscribers. If you have someone in mind who would benefit from our content, please do share.
To subscribe: here